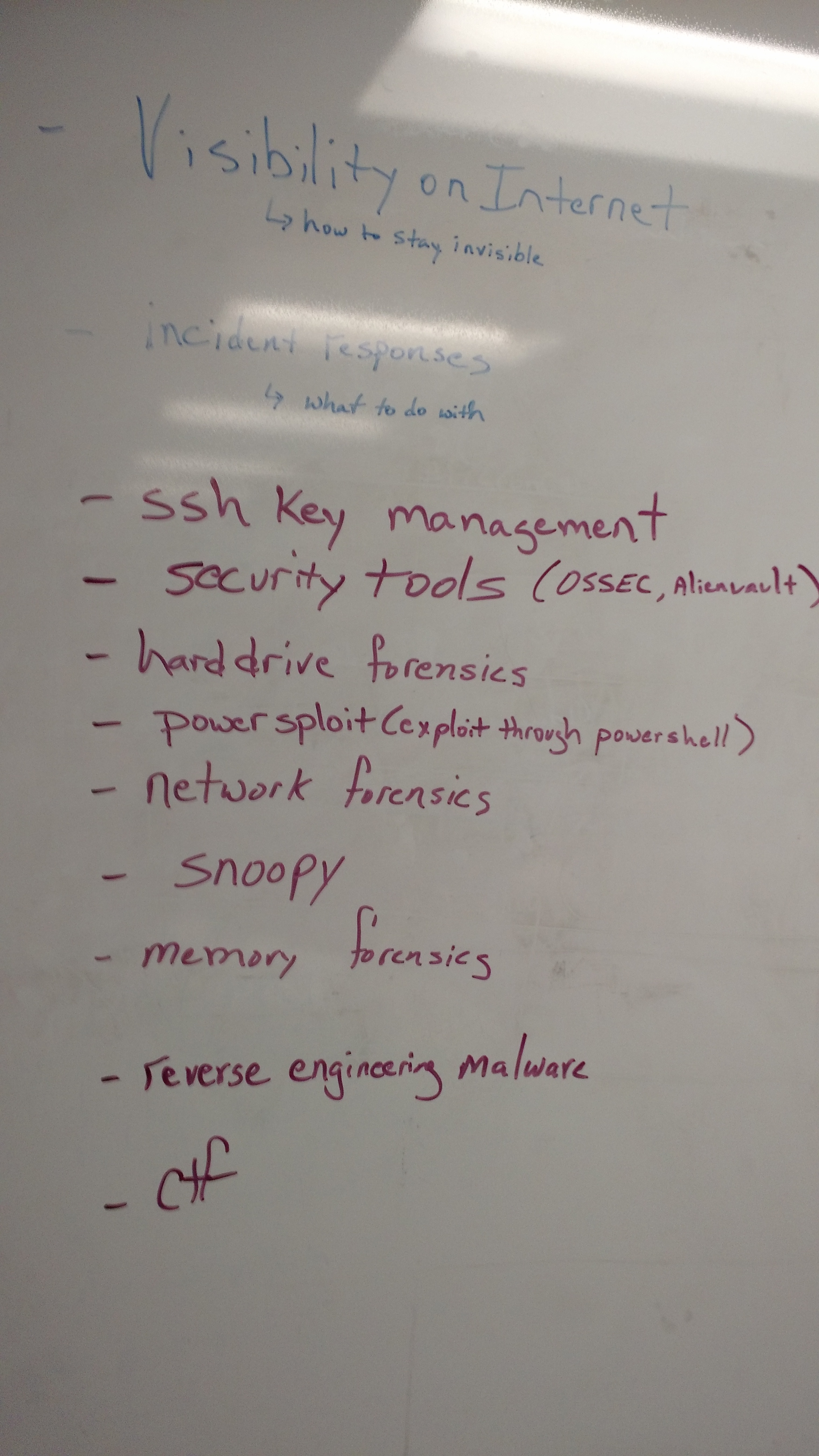
April 19, 2016, meetup agenda - Fire Talks
Taken at BSides Nashville by Timothy De Block
Our next meetup is a week from today, April 19, 2016, starting at 6:00 PM at our new location, the USC/Columbia Technology Incubator. Details are located on our site (http://www.colasec.org/how-to-find-us/). If you have any questions on how to get there respond to this thread or contact Adam directly.
Our meetup agenda will include our usual intro plus a recap of BSides Nashville.Then we'll move into our four 15-minute Fire Talks for the evening.
Fire Talks
The Powerup your attacks with PowerShell - Ralph Collum
Abstract: We will cover a few PowerShell basics to get everybody warmed up. Then we will explore the hacking methodology starting with reconnaissance and moving through to Post Exploitation using PowerShell.
Using network flow records for good - Jeff Lang
Abstract: As part of real-time traffic monitoring and historic forensic investigations, Network Flow records can be an invaluable asset. Flow records are summary data about all the network traffic that is passing through your network devices to answer questions such as how many hosts are talking, whois is talking to whom, and how often? The main purpose of this FireTalk is to discuss common incidents that might occur on a network and show example Network Flow data for those incidents.
Cyber Horoscope of 2016 with a Focus on Ransomware - Jasun Tate
Abstract: A unorthodox approach at securing an organization from 12 positional facets, with an highlight on strategy deployment from the below:
- Threat Intelligence Manager
- Backup Manager
- CXO
- CISO
- Front End Developer
- Compliance Director
- Human Resources
- Configuration Manager
- Internal Audit
- Fraud Examiner
- Patch Manager
Fire Talk abstract slacker - Adam Twitty
Abstract: One of the fundamental problems with using the internet is that you don't know where it's been. Who owns the wire, the switch, the router, the server once data leaves your network? How do we protect this information?
This talk will explore the various methods and protocols that we use every day to protect our information and make sure that we know who we are talking to. You'll also learn what the difference is between encoding, hashing, and encryption. Finally we'll explore some of the more obscure ways of obfuscating data that you might not have heard of before.
I'm looking forward to seeing you all there!